Spoof is a familiar term meaning parody or hoax, but it assumed a more negative flavour when it started to be used in the computer network world: here the term applies when an entity disguises itself as another the gain advantages: this is essentially done counterfeiting messages or signals.
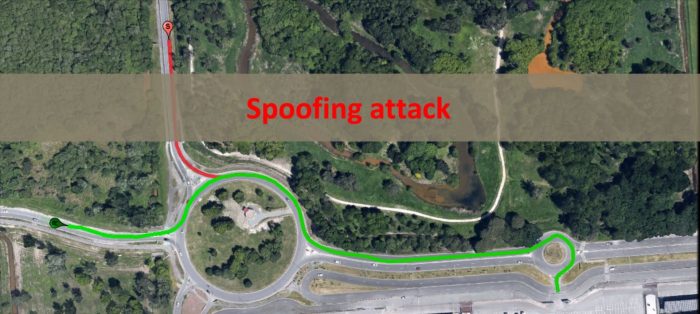
In the GNSS contest “spoofing” is the transmission of counterfeit GNSS-like signals, with the intent to produce a false position within the victim receiver without disrupting the GNSS operations.
Several possible implementation of spoofing attacks are well described in GNSS literature and they are often classified as simplistic, intermediate (or shadowed), and sophisticated. For the sake of completeness, it is worth to cite also a different kind of attack called “meaconing”. It is simpler with respect to the spoofing, because it doesn’t imply signal generation but just signal reception and delayed rebroadcasting. The word “meacon” is a portmanteau of masking beacon.
Despite the theory supporting the generation of such attacks is far from trivial, several attacks have been already reported. Among them, the black see one is the most discussed and documented: between the 22nd and 24th of June 2017, a number of ships in the Black Sea reported anomalies with their GPS-derived position, and found themselves apparently located at an airport. (http://gpsworld.com/spoofing-in-the-black-sea-what-really-happened/)
Galileo is going to implement a set of defences against these kind of attacks starting from the Open Service (OS). It will soon provide a Navigation Message Authentication feature, known as the Open Service Navigation Message Authentication (OS-NMA). This exploitation of this service will prevent the most likely spoofing attacks to succeed in fouling GNSS receivers; in fact, via this feature, users can verify that a navigation message comes from a Galileo satellite and not a potentially malicious source. The Open Service is the Galileo programme’s free service for positioning, navigation and timing.